# 通达OA v11.6 任意文件删除&RCE
## 漏洞描述
通过任意文件漏洞删除上传点包含的身份验证文件,从而造成未授权访问实现任意文件上传
## 漏洞影响
> [!NOTE]
>
> 通达OA v11.6
## 环境搭建
[通达OA v11.6下载链接](https://cdndown.tongda2000.com/oa/2019/TDOA11.6.exe)
下载完毕点击安装即可
## 漏洞复现
使用解密工具 SeayDzend(zend解密工具) 对通达OA的加密代码进行解密
> [!NOTE]
>
> 解密工具已经放在目录下的POC目录中
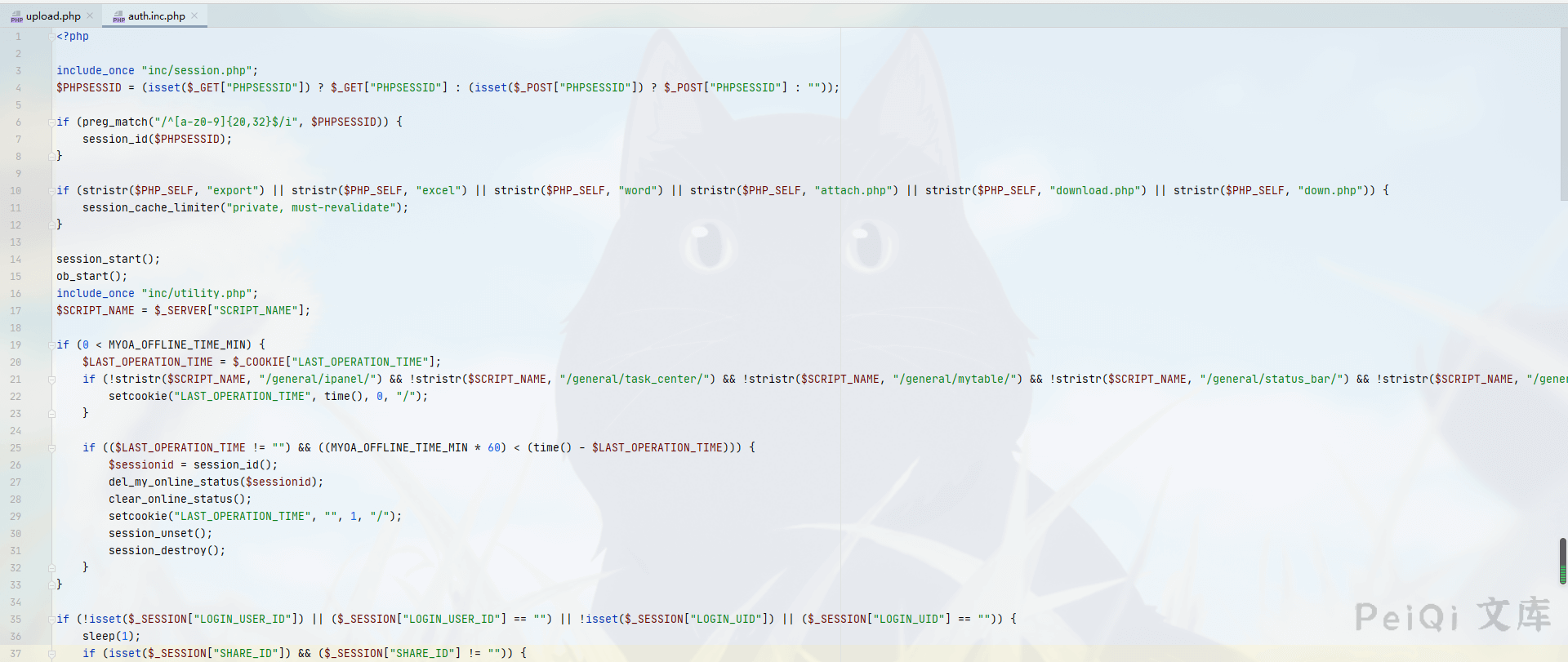
解密完成后查看 **webroot\general\data_center\utils\upload.php** 文件
“`php
\r\n